- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
- [email protected]
Poorly written article with little substance but a zinger of a headline. Think they’re trying to take advantage of announcements of Intel and TPM security flaws in the past to get more clicks.
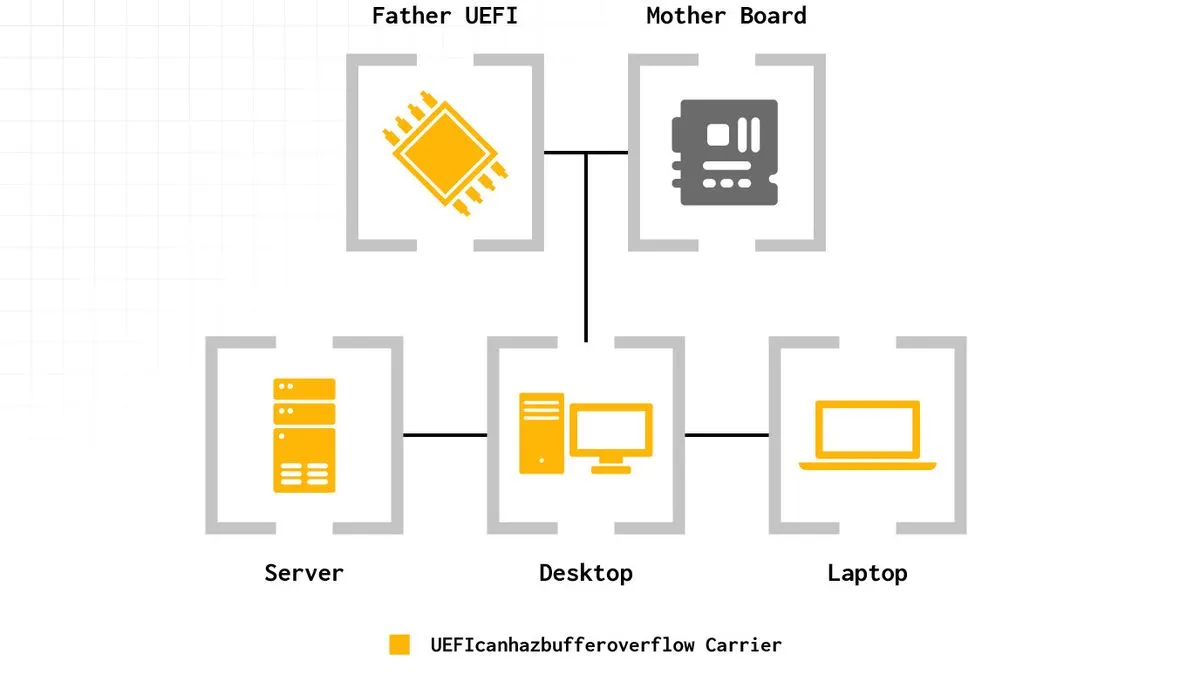
This is a UEFI firmware issue that can be patched by BIOS vendors. It is an issue at a very low level, but not an issue with Intel or the TPM.
The exploit is in the UEFI firmware code for handling the TPM and used for privilege escalation in that firmware, “TPM won’t save you” doesn’t really make sense because no shit. The vulnerability doesn’t mean the TPM unseals its contents though, and I’m curious if the exploit modifies the PCR values enough that OS security could trigger (Bitlocker recovery and whatever). Wouldn’t help if the malicious software was already there though.
phew! good thing I still have a few 386sx AMI BIOS boards handy. no ones shopping around zero days on those anymore, right?
Does TPM do anything ?
If you disable it you can prevent Microsoft from force updating your windows 10 install to windows 11. Obviously a play to get people to buy new hardware for 11 but a useful anti feature I suppose until you can stomach switching to Linux.