I watched a couple really interesting talks from this past Def Con. In one of the talks, Snoop Unto Them As They Snoop Unto Us, Null Agent points out that all Axon equipment (the company putting tasers on drones) share the same organizationally unique identifier (OUI) and communicate via Bluetooth Low Energy. When you pull your firearm or taser from an Axon holster, it can be set up to signal your bodycam to automatically turn on, for example. So by snooping on the BLE data channels you can look for Axon’s OUI and infer that a law enforcement officer is within your Bluetooth range (max 300ft or so in optimal conditions).
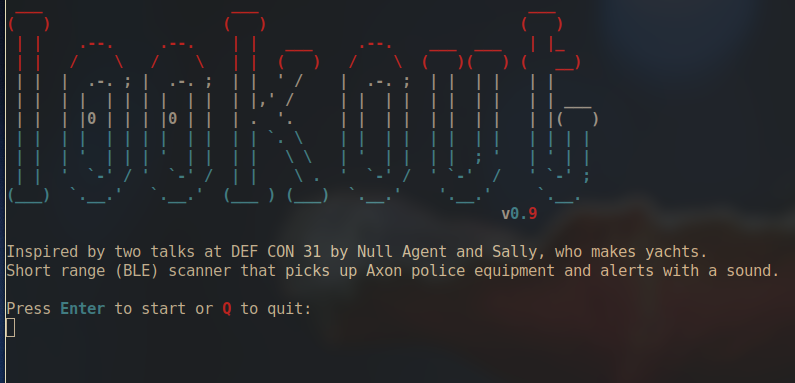
That’s all this script does. If it detects Axon equipment it plays a sound, alerts on your terminal, and logs the MAC address / time of encounter. I run it on my laptop in my living room with a super cheap Bluetooth adapter and I get notified when there are cops outside. Couple this with listening to your local police / public safety radio and you’ll never be surprised by a no-knock again.



A company reusing “pre-existing tech” doesn’t really seem to be the issue here. Were they supposed to invent a whole new communication protocol for this use case?
The issue I see is that they didn’t bother to obfuscate the MAC address of their BLE equipment. Maybe there is a reason they’re not allowed to change the OUI of their BT transmitter?