If they don’t understand this, can we even call it intelligent life?
Maybe they use Emacs.
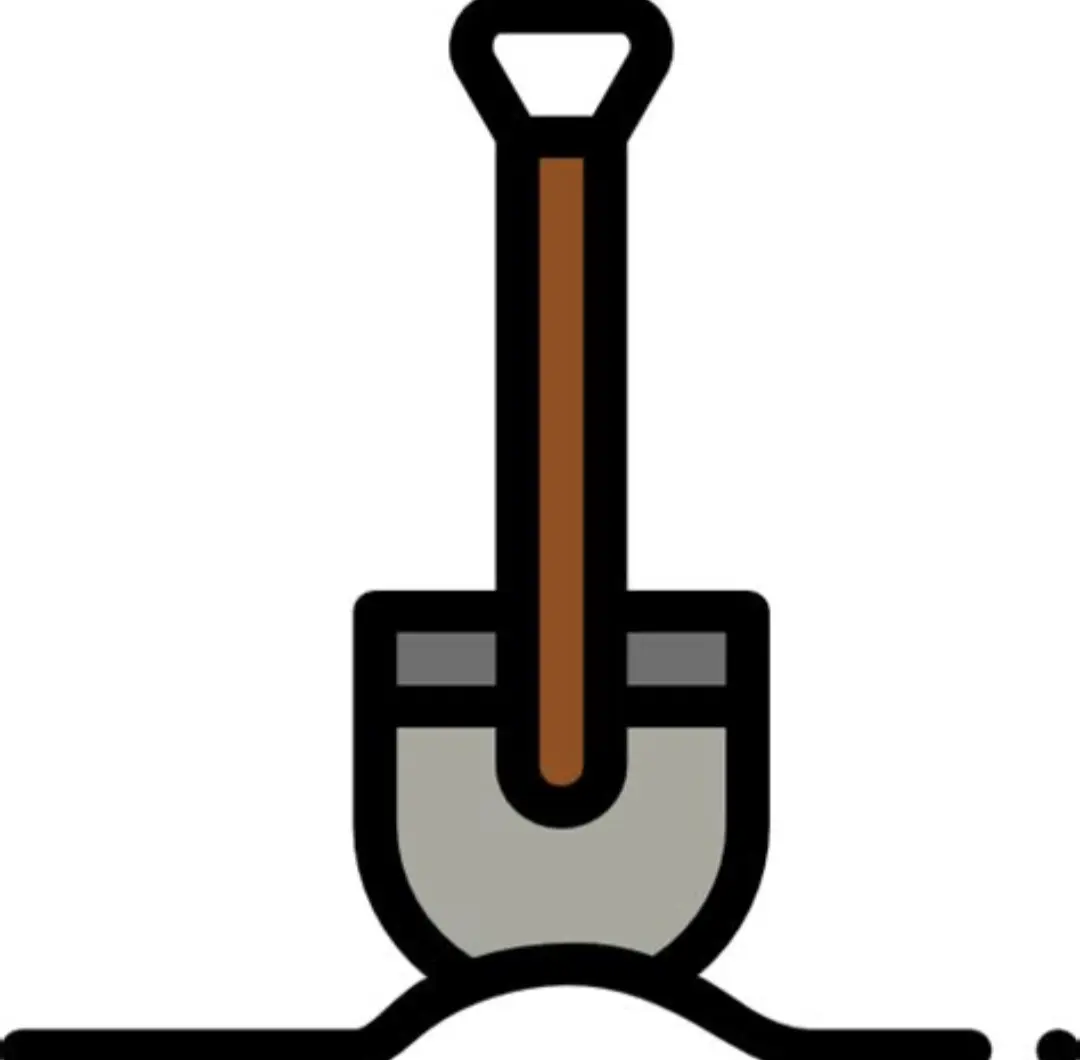
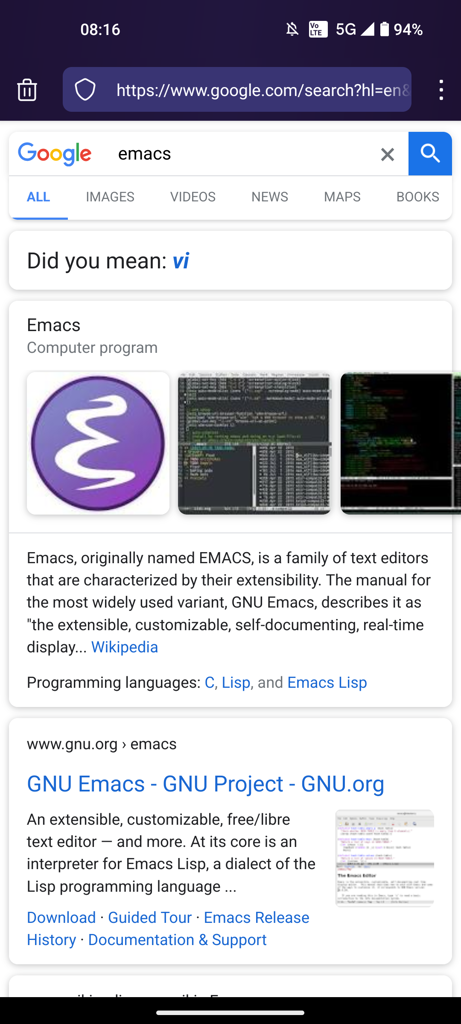
Bonus: I googled “emacs” to make sure I got the capitalization right for the post and Google is throwing shade:

Google does the opposite of “vi”. Some people just like to watch the world burn.
I misread “the world bum”
The term “keming” is sometimes used informally to refer to poor kerning (the letters r and n placed too close together being easily mistaken for the letter m).
Nano forever!
edis the standard text editor.
Holy shit lmao
It’s the other way around, too.
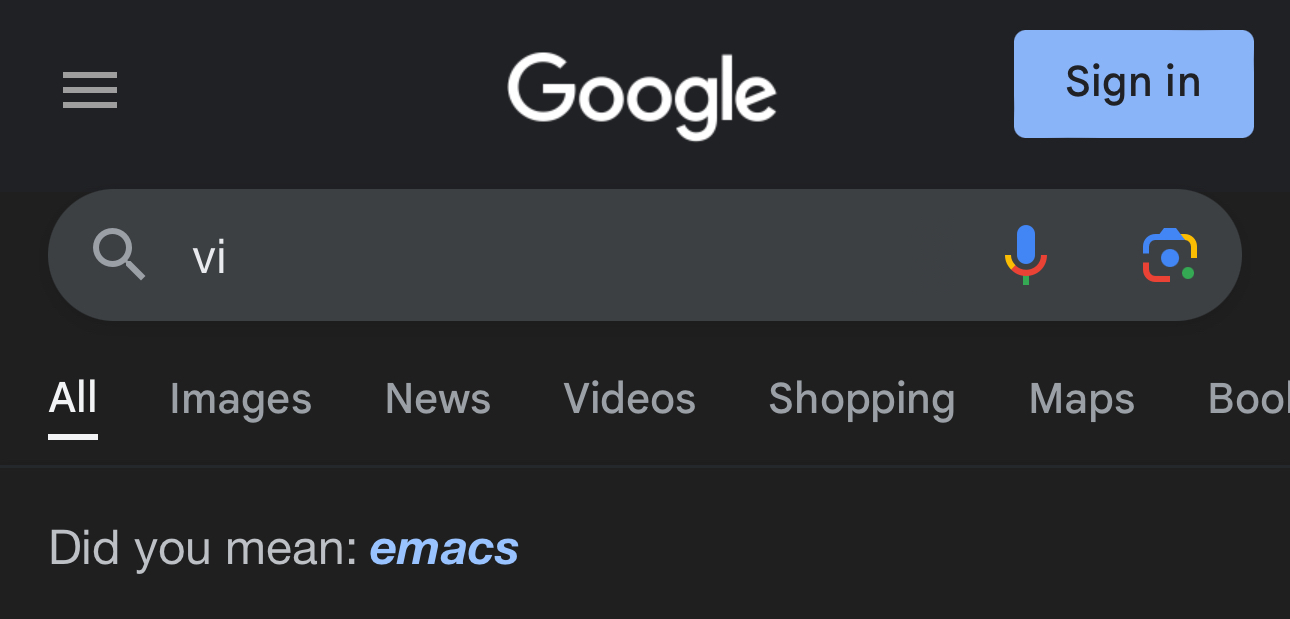
Not as true though.
This gotta be some inside joke leaking from google
Maybe it’s time to stop using GOOG
oof
Just capitalize it EMACS and people will think you’re more senior than in reality
I don’t know how people get this. I tried but it didn’t do this.
Strange, I just tried and got the vi suggestion. And, googling vi gave me an emacs suggestion. So shade all around!
Maybe they use Emacs.
Exactly
Well, then my point still stands.
Jk, don’t hurt me please!
Truth
I just shoot myself whenever I want to leave vim
You don’t need to be so drastic just shut down the electricity by the main switch
I rent a place where I don’t have direct access to the main switch, so what I do is I just stop paying utilities until Vim closes :)
Or just shoot the main switch if you at least have a line of sight on it
you can just unplug your pc: and that way you won’t incur downtime for the rest of the house.
You haven’t shot yourself yet though so you’re still in vim
You don’t know!
wrong: you press esc multiple times to make sure you are in normal mode.
At least 3 times. 5 to make sure.
sudo nano
You shouldn’t really use editor with sudo, but instead use sudoedit to edit files restricted to root user
SUDO_EDITOR=nano sudoedit /etc/fstabThis accomplishes the same function while running the text editor as unprivileged user
Why?
Files from user: nano
Files from root: sudo nano
Files from another user: sudo nano (and if new sudo chown after)… 😂
Never had any problems with this in over 10 years… 😅😂
Doing
sudo nanowill not load your user configuration,sudoeditwill. I had plenty of problems with this, but I assume you don’t have any custom configuration.One reason why sometime I don’t do sudoedit is that I make a lot of changes to the config/restart service/see it works/edit etc… sudoedit only write to the file when exiting, so that flow won’t work…
for example when having adding a new host on nginx and some configuration and see if everything work (sudo vim/systemc nginx restart/curl https:// domain loop)
but yeah in general i’ll just use sudoedit (which alias to se for me) for my root editing
I just have a root custom config too. 🤷♂️ This even allows me to easily use different configs for root than for the user.
Made with ‘sudo nano’, fyi. 😂
As mentioned, to prevent running your text editor with root permissions. It’s just security optimization
Let me rephrase my question:
Why would I not want to open nano as root?
No offense, but that sounds like more OCD behavior. 😅 I don’t need or want protection against myself, and I even loath the whole “that’s not how you’re supposed to do it”-mentality of linux (where when commands know very well what you want, instead of doing it, just tell you you forgot something). 😅
deleted by creator
But, in that example:
If I’m the admin it doesn’t matter I use it.
If I’m not it’s not my problem that I could get more privileges than allowed. I’d probably even use the possibility then. 😅
So it poses a risk if you allow none-admin users to do that on your system, but I still don’t see why I must choose to not use nano as root myself. 😅
Anyway, good practice to me is ease-of-use instead of with 7 protections against things that rarely happen.
Like, I’m pretty sure you are better protected from burglars if you also lock all doors inside your house, but I’m definitely not doing that either. 😅
Edit: Also, if you have users on your system, just chroot/vroot/lxc them, so they be free to ‘sudo nano’ too… 😅
deleted by creator
It’s not any OCD behavior, but simply the best practices. You’ve probably at least minimally familiar with the principal of least privilege? The idea is to minimize scope of a potential problem , was it malicious attack or user error, by restricting access to minimum required to perform a task. It may feel like fighting pedantically (and I’ve been fighting this more than I’d care to) but it will save your ass one day.
It’s probably to protect against any potential security vulnerabilities in the text editor program itself, not to protect you from yourself.
Wouldn’t that logic count for anything, including sudo itself?
Sure, but sudo is specifically designed with security in mind as a security program, whereas text editors are not (although I am more likely to trust vim than vscode). Running a malicious program as the user and not as root can help mitigate the impact it could do, even though it will still be able to do a lot as a user.
You can say that just about anything.
sudo grub sudo boot sudo root=/dev/disk/linux sudo kernel-6.1.image sudo init sudo elogind sudo xterm sudo bash sudo nano
Again, like I replied to the other comment, most of the programs you need root for are designed with security in mind and are inherently more secure and have less vulnerabilities than a non security focused program (that is not to say that it is impossible for a security program to have vulnerabilities -it certainly occurred before and keeps occurring- they just have a lot fewer). But even if you need root permissions for a non security focused program, you still shouldn’t let any program have it, the whole point is to minimize the surface of attack.
Alternatively you could use my favorite approach, Visual Studio Code. Just open the file with it, edit it and upon saving you will be promoted if the file needs admin rights to save.
Okay but how can I show how good I am with shortcuts to edit legacy software ?
Vscode does have a lot of shortcuts, so you could always study them in detail and impress others that way. 😅
Yup, s/vsc/kwrite/ personally, it’s lighter, but why shouldn’t I have a pretty for my config editing needs…
I love vsc but it’s not always available.
So for any supposedly malicious activity (infected) it wants to do, it just has to hold until you save and give admin access? 😅
Yes, but if you want to argue along those lines, you could also have an infected version of vim on your system just waiting to do malicious stuff until you give it sudo access.
Indeed… Hence why I use ‘sudo nano’. 😜
until the moment you realize that somehow you are not on your native keyboard layout and where the hell is : and ! in this weird language??!
ESC Z Z
I have done this too many times now lol, you’d think I would have learned
“I use Arch Linux btw”
*doesn’t know how to use vim
Pottery
Hey!
ESC Z Z
Although I usually bang ESC a few times to
make sure i’m back to command modeyou mean normal mode?
Yes, I do.
Double Z’s will save and then exit. The command on until board will exit without saving changes.
yeah to exit without saving you do ZQ instead of ZZ
Shouldn’t be Z Z esc ? Because, you know ZZ top.
deleted by creator
I think you meant :r!:() :;:
Great, now all my changes are lost. Thank you very much!
Your welcome!
wq
Thanks Sherlock.
Yanks power cord
deleted by creator
Slumps up the yummy battery acid
Ctrl-z
ps
kill -9 pid
fg
Alternative:
Ctrl-z kill -9 %1 # Shell keeps track of job pids for you, job 1 is %1, job 2 is %2, etc fg # Not technically necessary, but it's fun to see the corpsekillall vimReminds me of the time I brought down a whole AIX server with the
killallcommand back in the 1990s.On AIX
killallreally means kill every single process.
Ok ok, I know it’s a meme, but gentle reminder that :x is :w and :q combined (save and exit). I got taught that in high school (it was a dec unix with real vt120 terminals) and luckily for me I remembered that even if I didn’t touch vi for a few years afterwards.
Funnily enough, I knew of :x before :w.
i think you mean ctrl s and ctrl x
That didn’t work
Still on it!? Are you, people, immortal? =)
nano is forever
What is this sorcery?! I thought you had to reboot each time to exit.
That’s only if you don’t want to save first (ahem write the buffer).
Odds are if you don’t know how to exit vim you probably don’t want to save whatever you wrote in there.
Who in there right mind would want to save a bunch of gibberish
ihh splqqiq:wq
Wear your mistakes proudlyq!