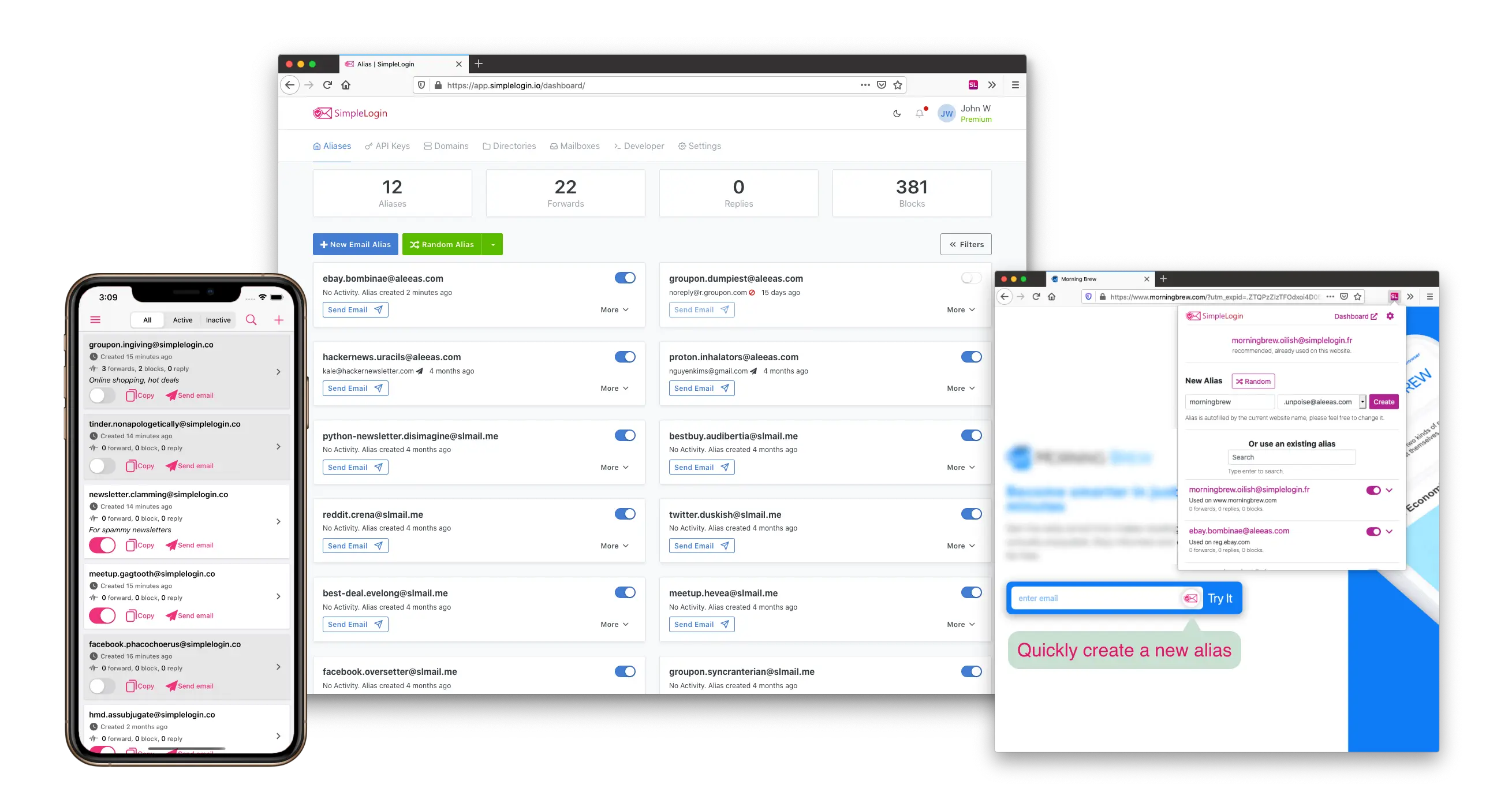
Email aliasing is one of the most underrated privacy techniques that has yet to go mainstream. For the privacy-conscious user, it offers a degree of separation between all your accounts, making it harder for data brokers to correlate your various accounts across different services by not using the same email address to sign up. For security, the same technique can also help defeat credential stuffing while obscuring your true email address, which is the central hub where all your identities can be managed (and the email address itself is literally half of the login information a would-be attacker would need to attempt to login). Your inbox is a critical thing to protect since a breach can offer information about additional accounts you have (via the emails already sitting in your inbox like updates, notifications, sign-in verifications, etc) as well as allowing an attacker to simply hit “reset password” on websites where you already have an account and thus take them over. As for mainstream users, the biggest advantage is probably the ability to manage spam more effectively – particularly from companies who refuse to respect opt-out links – from a single inbox, rather than having one inbox for professional use, then logging out and back into another for online shopping, then another for personal or newsletters, and so forth or simply having to give up and hope the spam filters don’t falsely flag anything important (or let junk though). Email aliasing makes effectively managing and controlling your inbox incredibly easy. With that in mind, this week, let’s examine some popular email aliasing services that the privacy community has to offer.


+1 for SimpleLogin. Not affiliated, just been using it for a few years now and it’s been rock solid and a complete game changer.
As an example someone tried a banking scam on me, and I asked them to read back the email address associated with my “bank account”, and they instead read back the alias I’d used on some other random website I’d put my credit card number into 6 months prior. This proved what website leaked my credit card, but also they were trying scam me (as if the request for a 2fa code wasn’t proof enough)